Page History
...
| Info |
|---|
IDERA Dashboard must be installed prior to performing this task. |
IDERA users in In environments that have not yet added a certificate signed by a Certification Authority (CA), IDERA users receive a warning message in their browser each time they attempt to open the SSL version of the IDERA Dashboard. Note that the default certificate provided with an IDERA product is not signed by any well-known CA and is intended only for use in testing purposes ONLY.
You can resolve this issue by adding a signed CA using the steps provided in Run IDERA Dashboard over TLS (HTTPS), or you can use the following steps to resolve this issue at no certificate cost.
Adding a self-signed certificate
Creating a Certificate
Create a self-signed certificate
- Launch Windows Powershell as administrator.
Create your certificate by running the following command. Leave Windows PowerShell open.
Code Block language powershell $certName = "{certificateName}" ## Replace {certificateName}Tip Replace
{certificateName}with the name that you will use to access the IDERA Dashboard. For example, if you are using thehttps://ComputerName:9291link to access IDERA Dashboard, then useComputerName. In case, you are using thehttps://ComputerName.Domain.com:9291address then useComputername.Domain.com. In this example we are usinglocalhost.Run the following command to configure your certificate settings.
Code Block language powershell $Params = @{ "DnsName" = @($certName,"{certificateName}") ## If you want to include other addresses or servers, you must separate each with a comma "CertStoreLocation" = "Cert:LocalMachine\My" "KeyExportPolicy" = "Exportable" "KeySpec" = "Signature" "KeyUsage" = @("KeyEncipherment","DigitalSignature") "KeyAlgorithm" = "RSA" "KeyLength" = "2048" "HashAlgorithm" = "SHA256" "NotAfter" = (Get-Date).AddYears(10) } ## Checks for asterisks in the $certName and replaces it with the underscore character If ($certName.Contains("*")) { $certName = $certName -replace '\*','_' }Note Replace
{certificateName}with the certificate name you previously defined in Step 2.Tip Change the
NotAfterparameter value to make your certificate valid for a more extended period.Run the command below to create your certificate defined with the parameters above.
Code Block $cert = New-SelfSignedCertificate @Params
| Anchor | ||||
|---|---|---|---|---|
|
Once the certificate is created, you need to export the certificate's private key. To do so, follow the steps below:
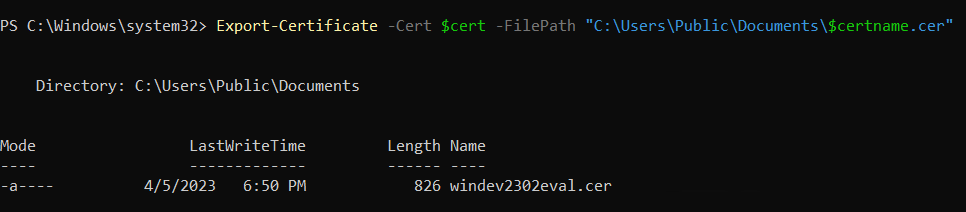
Export your certificate in
.cerformat by running the following command.Code Block language powershell Export-Certificate -Cert $cert -FilePath "{DesiredPath}\$certname.cer" ## Replace {DesiredPath} with the desired location e.g. C:\Users\Public\DocumentsOnce the certificate is created, you should be able to check the certificate specifications.
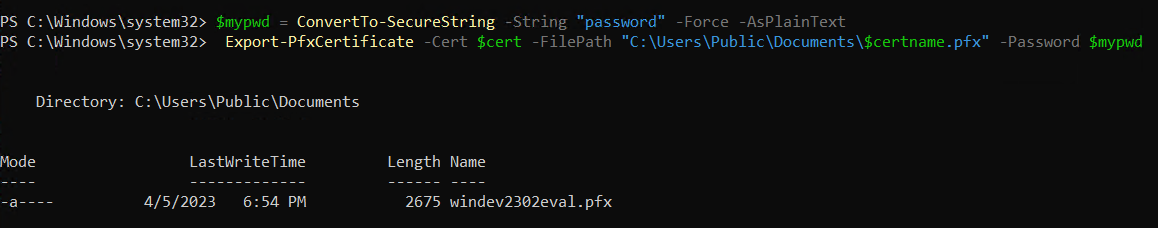
Create a password for your certificate private key and save it in a variable. Replace
{myPassword}with the password that you wish to use to protect your certificate's private key.Code Block language powershell $mypwd = ConvertTo-SecureString -String "{myPassword}" -Force -AsPlainText ## Replace {myPassword}Run the next command to export your private key, use the password you store in the
$mypwdvariable.Code Block language powershell Export-PfxCertificate -Cert $cert -FilePath "{DesiredPath}\$certname.pfx" -Password $mypwd ## Replace {DesiredPath} with your desired location e.g. C:\Users\Public\DocumentsWhen the private key is exported in a
.pfxfile, you should be able to check the certificate specifications.
Import your private key into the Trusted Root Certification Authorities
Complete your certificate configuration by adding the .cer file to the Trusted Root Certification Authorities folder in the Console Root. To do so, follow the steps below:
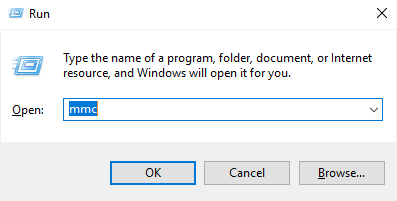
- Open the Microsoft Management Console (MMC) by selecting Start > Run and typing mmc. Click OK.
- When the MCC window opens, click File from the menu toolbar, and select Add/Remove Snap-in...
- Select Certificates from the Available snap-ins options and click Add >.
- In the Certificates snap-in window, select Computer Account, and click Next.
- In the Select Computer window, verify that Local computer is set as the computer you want the snap-in to manage. Click Finish.
- Import your certificate (
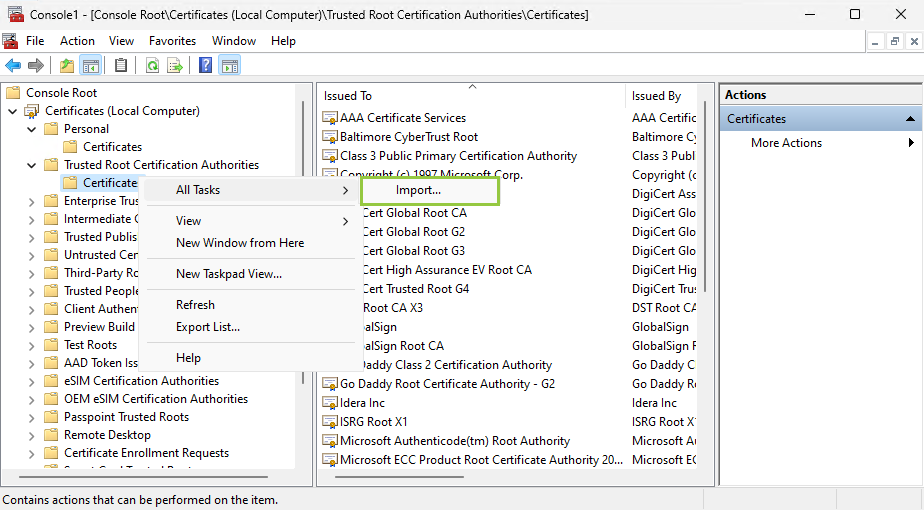
.cerfile) into the Trusted Root Certification Authorities folder. To do so, expand Certificates and right-click the Trusted Root Certification Authorities folder. Click All Tasks > Import...
Follow the Certificate Import Wizard instructions to import the
.cerfile previously created.Info When adding your certificate or private key using the Certificate Import Wizard, use the password you previously defined in the Export your certificate private key section.
Import Key Pair
- Download the free KeyStore Explorer utility from
and install it.Newtab2 alias http://keystore-explorer.org/ url http://keystore-explorer.org/ - Open KeyStore Explorer as administrator. On launch, it may ask you to download an updated Java Cryptography Extension (JCE) Unlimited Strength file.
- Click Open an existing KeyStore.
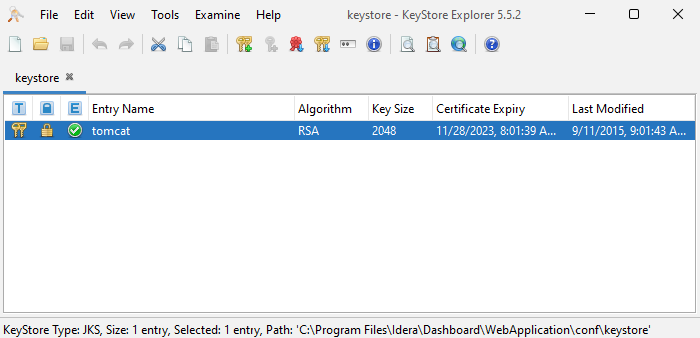
- Browse to the IDERA Dashboard conf directory (the default path is
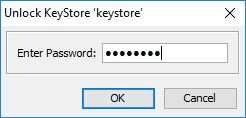
C:\Program Files\Idera\Dashboard\WebApplication\conf), and open the keystore file. - On the Unlock KeyStore dialog window, enter "password" and then click OK.
- KeyStore Explorer displays a list of any existing certificates. Delete the existing key and click the Import Key Pair button.
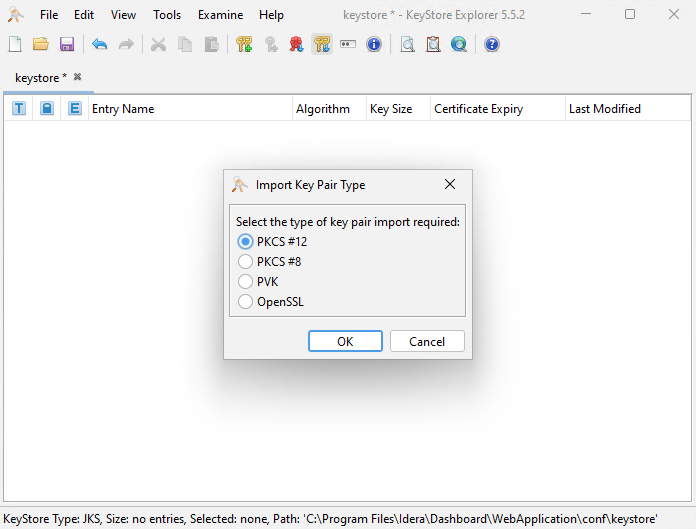
- Select PKCS #12 as the type of key you want to import, and click OK
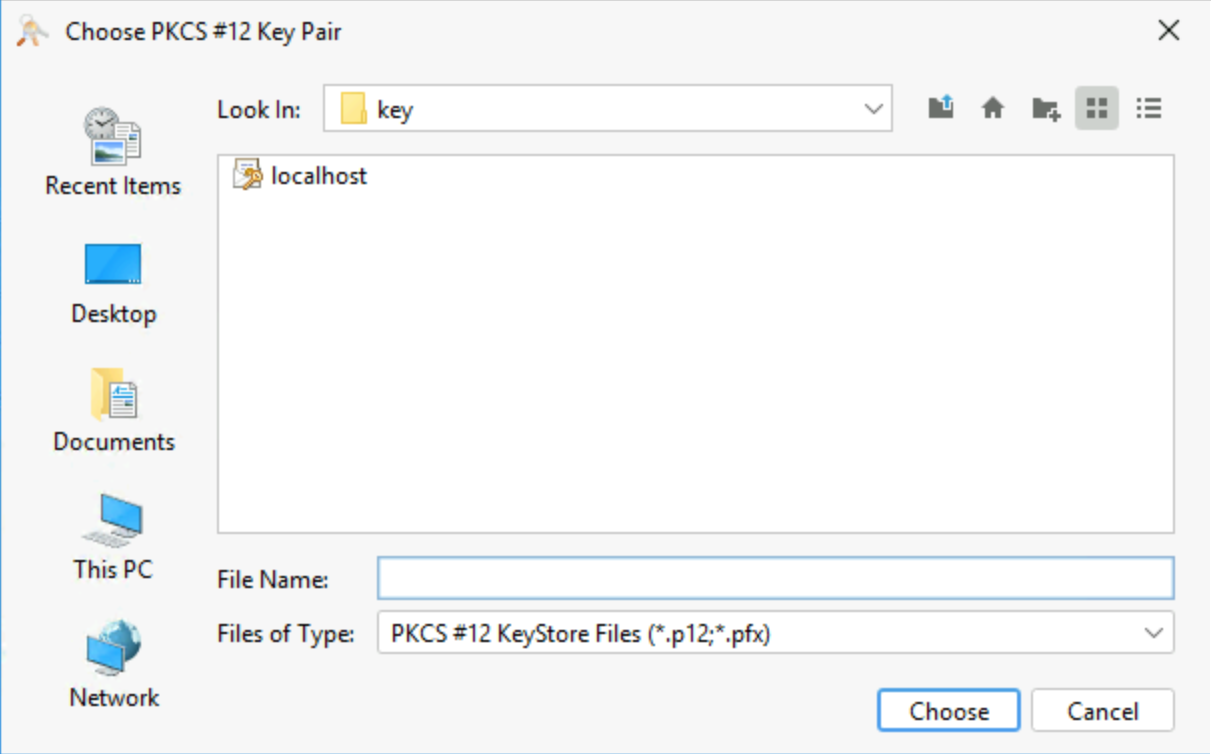
- Look for the key you created steps above (in this case,
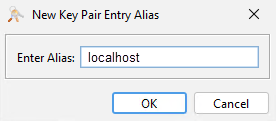
localhost.pfx) andclick Choose. - Select an alias for your key, and click OK.
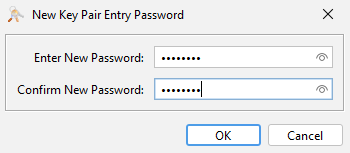
- In Enter New Password type "password", confirm, and click OK.
- When the configuration is completed the following message pops up, click OK.
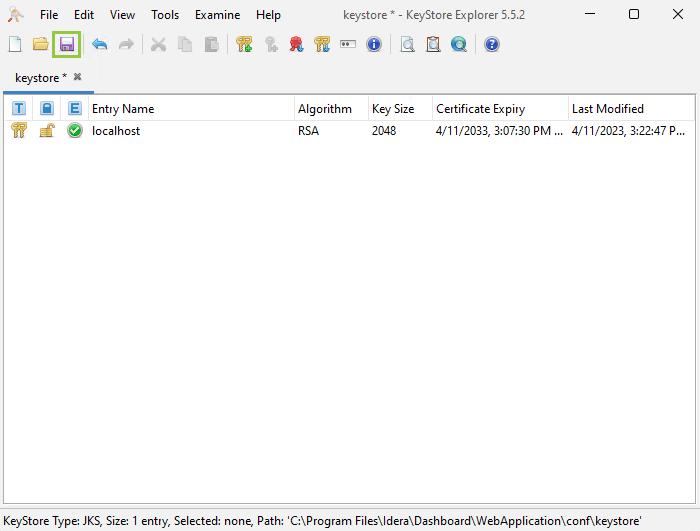
- Return to the main KeyStore Explorer window, save your configuration, and close the application.
- Close all the opened browsers.
- Restart
- Download the free KeyStore Explorer utility from
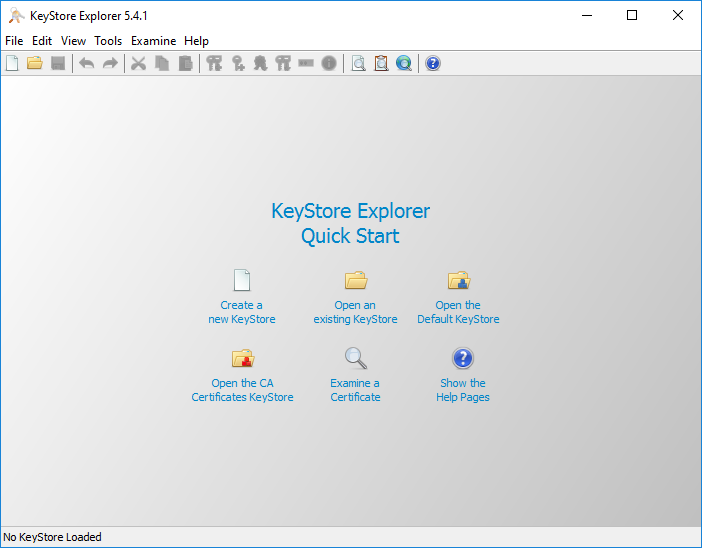
and install it.Newtab2 alias http://keystore-explorer.sourceforge.net/ url http://keystore-explorer.sourceforge.net/ - Open KeyStore Explorer. KeyStore Explorer displays the following Quick Start options. On launch, it may ask you to download an updated Java Cryptography Extension (JCE) Unlimited Strength file.
- Click Open an existing KeyStore.
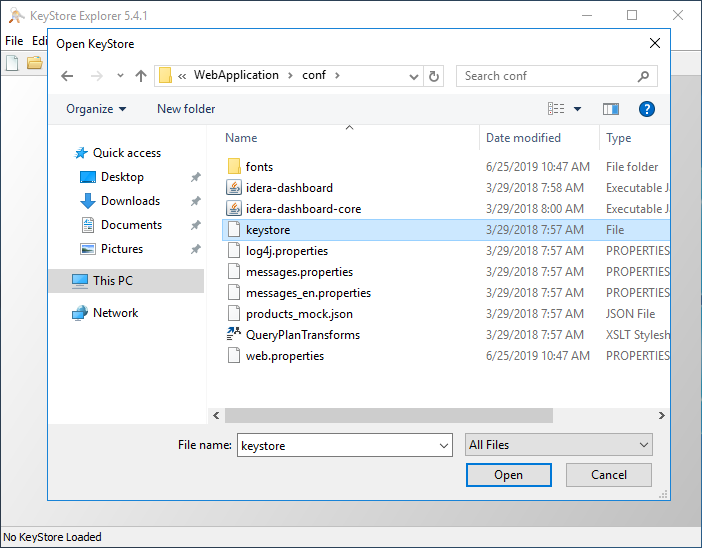
- Browse to the IDERA Dashboard conf directory, the default path is
C:\Program Files\Idera\Dashboard\WebApplication\conf, and open the keystore file. - On the Unlock KeyStore dialog, enter "password" and then click OK.
KeyStore Explorer displays a list of any existing certificates. - To create a new key click Generate Key Pair.
- On the Generate New Pair Certificate window, make the following changes:
- In the Signature Algorithm list, select SHA-1 with RSA or SHA-256 with RSA. This example uses SHA-1 with RSA.
- In the Validity Period field set the number of years the certificate is valid, this example uses 5 years, and click Apply.
- Click the Edit Name button to open the Name window.
- On the Generate New Pair Certificate window click Add Extensions.
- On the Add Certificate Extensions window, click Add
- On the Add extension Type dialog select Subject Alternative Name and click OK.
- On the Subject Alternative Name Extension dialog, click the Add .
On the Alternative Name dialog, select DNS Name. In the General Name Value field, enter the Fully Qualified Domain Name of the server on which the IDERA Dashboard exists. Click OK on all windows to save your changes.
- On the New Key Pair Entry Alias dialog, verify that the displayed alias matches the name of your website and then click OK.
KeyStore Explorer displays the New Key Pair Entry Password window. Type and confirm the password you want to use for the key pair, and then click OK.
Note This password must match the password entered in step 5.
In this case, type the following password in both input boxes:
password- Verify the new line in the KeyStore Explorer certificate list, as shown in the following image.
- To delete the old certificate select the appropriate line, and then click Cut. If you get a Pasword requement use the one from step 5.
- Save the changes to the keystore file.
- Double-click on the certificate that you created, verify your details, and click Export.
- On the Export Certificate dialog save the certificate in the IDERA Dashboard conf directory (e.g.
C:\Program\Files\Idera\Dashboard\WebApplication\conf\) - Return to the main KeyStore Explorer window and close the application.
- Restart the Idera Dashboard Core Service and Idera Dashboard Web Application Service.
KeyStore Explorer begins to generate a new key pair
In essence, the name that you provide should match the URL that you intend to use. For example, the following image shows an entry that creates a certificate for https://localhost. For more information on each field refer to
| Newtab2 | ||||
|---|---|---|---|---|
|
Once you fill your information click OK.
Adding a certificate
...
| Newtab2 | ||||
|---|---|---|---|---|
|
- Access to IDERA Dashboard with the following link
https://<{certificateName}>:9291.