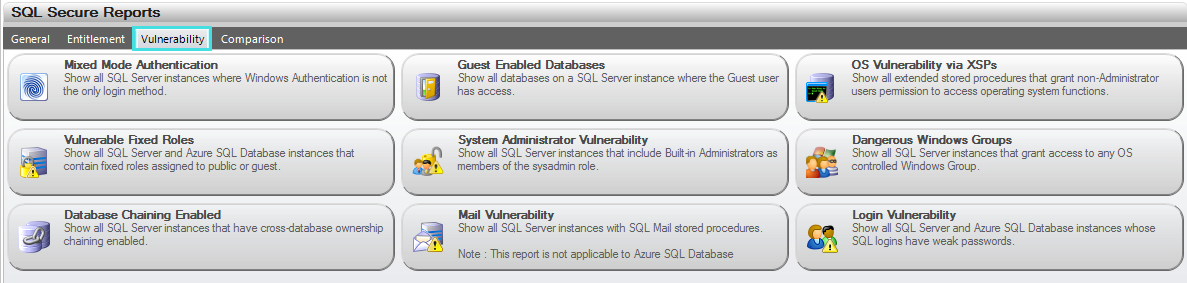
| Report Name | Report Description |
|---|---|
| Mixed Mode Authentication | Displays all SQL Server instances where Windows Authentication is not the only login method |
| Guest Enabled Databases | Displays all databases on a SQL Server instance where the Guest user has access |
| OS Vulnerability via XSPs | Displays all extended stored procedures that allow access to operating system features that could compromise system security |
| Vulnerable Fixed Roles | Displays all SQL Server instances that contain fixed roles assigned to public or guest |
| System Administrator Vulnerability | Displays all SQL Server instances that include built-in Administrators as members of the sysadmin role |
| Dangerous Windows Groups | Displays all SQL Server instances that grant access to any OS controlled Windows Group |
| Database Chaining Enabled | Display all SQL Server instances that have cross-database ownership chaining enabled |
| Mail Vulnerability | Displays all SQL Server instances with SQL Mail stored procedures |
| Login Vulnerability | Displays any SQL logins that have weak (easily guessed or hacked) passwords and lists their security properties, including the state of their password health. |
IDERA | Products | Purchase | Support | Community | Resources | About Us | Legal
Copyright © 2004-2024 IDERA, Inc.