IDERA users in environments that have not yet added a certificate signed by a Certification Authority (CA) receive a warning message in their browser each time they attempt to open the SSL version of SQLDM Web Console or Idera Dashboard. To access SQL Diagnostic Manager over HTTPS with a self-signed certificate you may need to enable SSL on the SQL Diagnostic Manager Rest service and add a certificate.
To access SQL Diagnostic Manager over HTTPS, you should add a certificate for SQLDM Web Console following the steps below:
Create your certificate by running the following command. Leave the PowerShell console session open.
$certName = "{certificateName}" ## Replace {certificateName} |
Replace |
Run the following command to configure your certificate settings.
$Params = @{
"DnsName" = @($certName,"{Param1}", "{Param2}") ## If you want to include other addresses or servers, you must separate each with a comma
"CertStoreLocation" = "Cert:LocalMachine\My"
"KeyExportPolicy" = "Exportable"
"KeySpec" = "Signature"
"KeyUsage" = @("KeyEncipherment","DigitalSignature")
"KeyAlgorithm" = "RSA"
"KeyLength" = "2048"
"HashAlgorithm" = "SHA256"
"NotAfter" = (Get-Date).AddYears(10)
}
## Checks for asterisks in the $certName and replaces it with the underscore character
If ($certName.Contains("*")) {
$certName = $certName -replace '\*','_'
} |
Replace |
Change the |
Run the command below to create your certificate defined with the parameters above.
$cert = New-SelfSignedCertificate @Params |
Once the certificate is created, you need to export the certificate's private key. To do so, follow the steps below:
Export your certificate in .cer format by running the following command.
Export-Certificate -Cert $cert -FilePath "{DesiredPath}\$certname.cer" ## Replace {DesiredPath} with the desired location e.g. C:\Users\Public\Documents |
Once the certificate is created, you should be able to check the certificate specifications.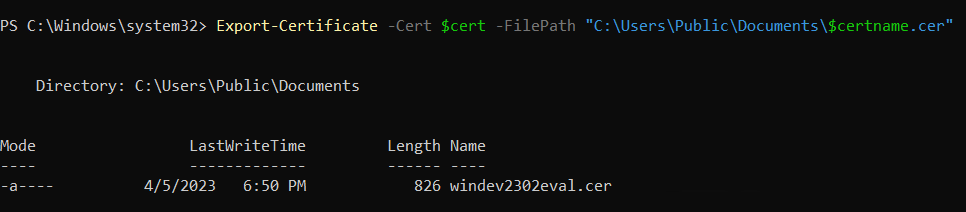
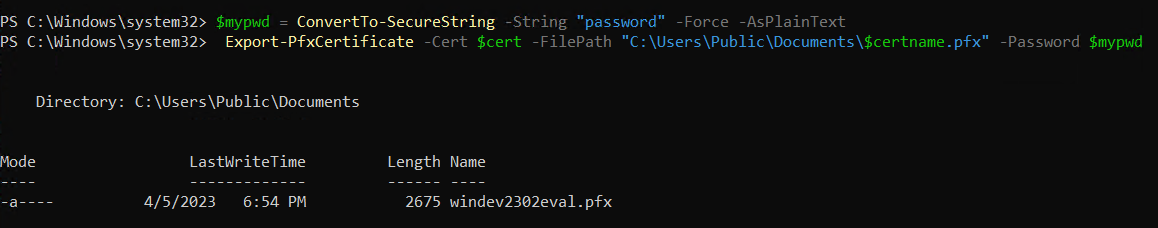
Create a password for your certificate private key and save it in a variable. Replace {myPassword} with the password that you wish to use to protect your certificate's private key.
$mypwd = ConvertTo-SecureString -String "{myPassword}" -Force -AsPlainText ## Replace {myPassword} |
Run the next command to export your private key, use the password you store in the $mypwd variable.
Export-PfxCertificate -Cert $cert -FilePath "{DesiredPath}\$certname.pfx" -Password $mypwd ## Replace {DesiredPath} with your desired location e.g. C:\Users\Public\Documents |
When the private key is exported in a .pfx file, you should be able to check the certificate specifications.
Complete your certificate configuration by adding the .cer file to the Trusted Root Certification Authorities folder in the Console Root. To do so, follow the steps below.
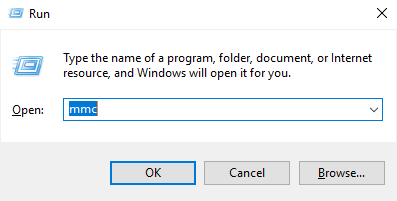
.cer file) into the Trusted Root Certification Authorities folder. To do so, expand the Certificates node, from the Console Root tree and right-click the Trusted Root Certification Authorities folder, select All Tasks, and click Import...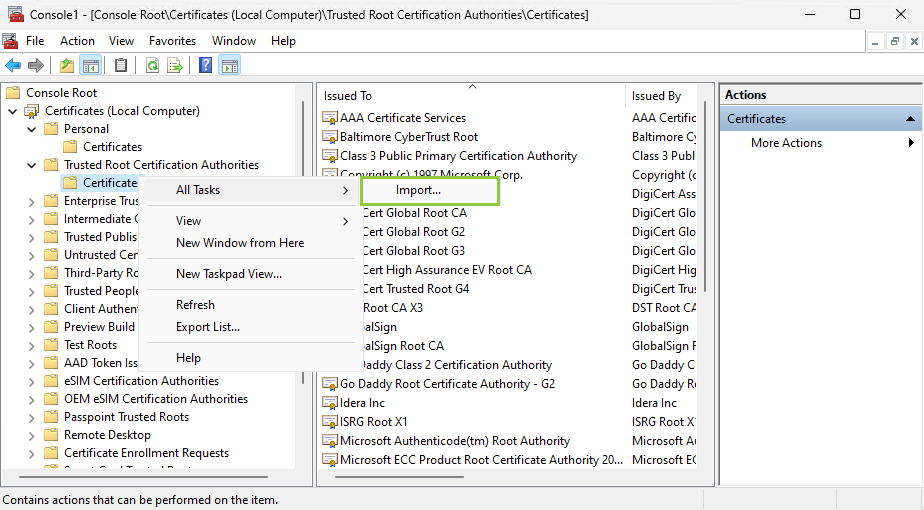
When the Certificate Import Wizard opens, follow the instructions to import the .cer file previously created.
When adding your certificate private key using the Certificate Import Wizard, use the password you previously defined in the Export your certificate private key section. |
Once the steps above are completed, copy the .pfx file into the Idera SQLDM Web Console UI directory.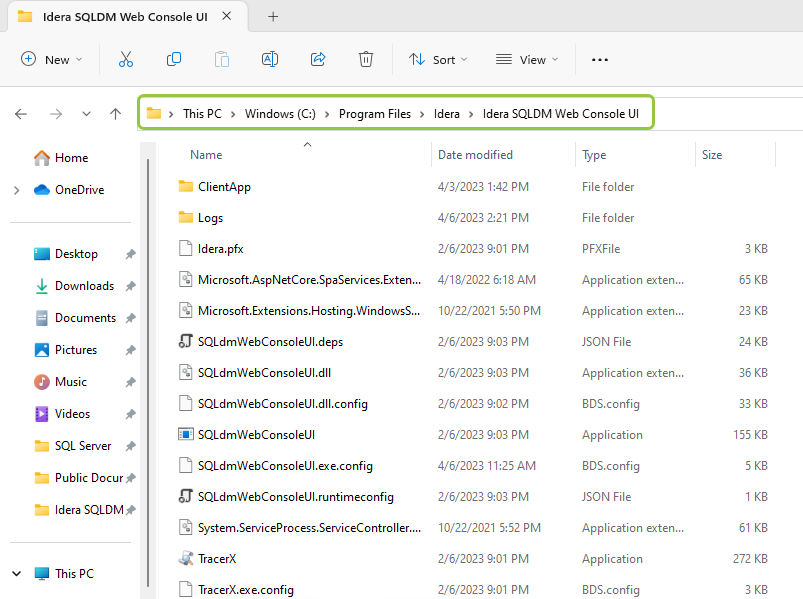
Open the SQLdmWebConsoleUI.exe.config file using any text editor, which should be launched using the Run as administrator.
ssl-cert and the cert-password tags and update them with the name and password of the certificate previously created.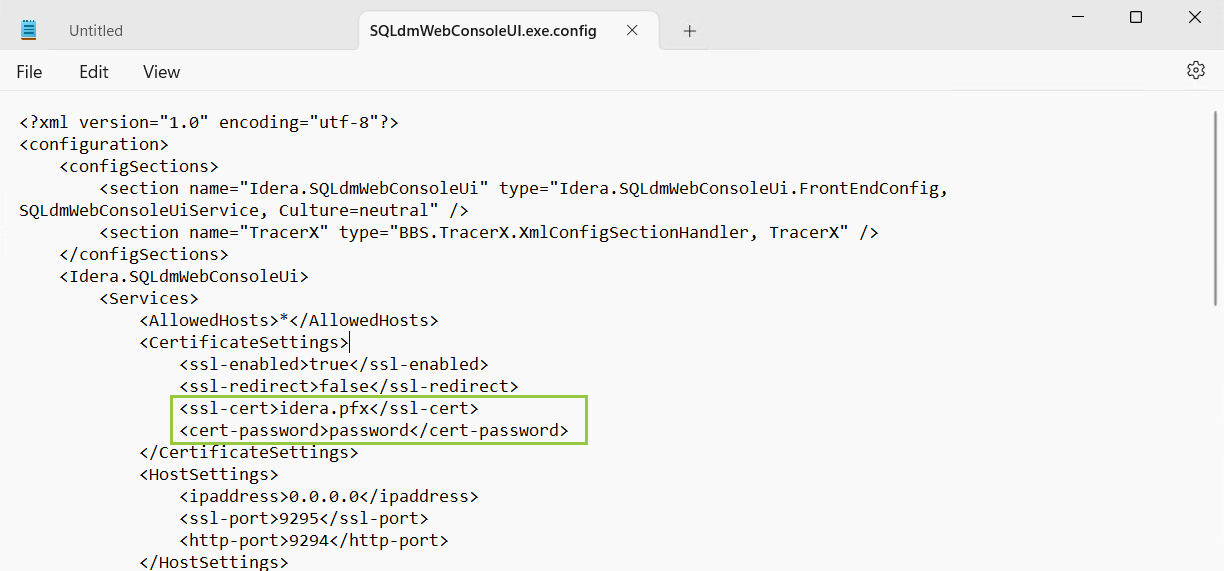
https://<certificateName>:9295/ In case you are working with Idera Dashboard, add a self-signed certificate as you have already completed the steps above, you only have to import the certificate key pair with Key Store Explorer. For more information about it, refer to Resolving the certificate error message. |
This section is only for users who use the Idera Dashboard Web Console. |
After creating a self-signed certificate for Idera Dashboard, follow these instructions to bind a certificate to SQLDM:
|